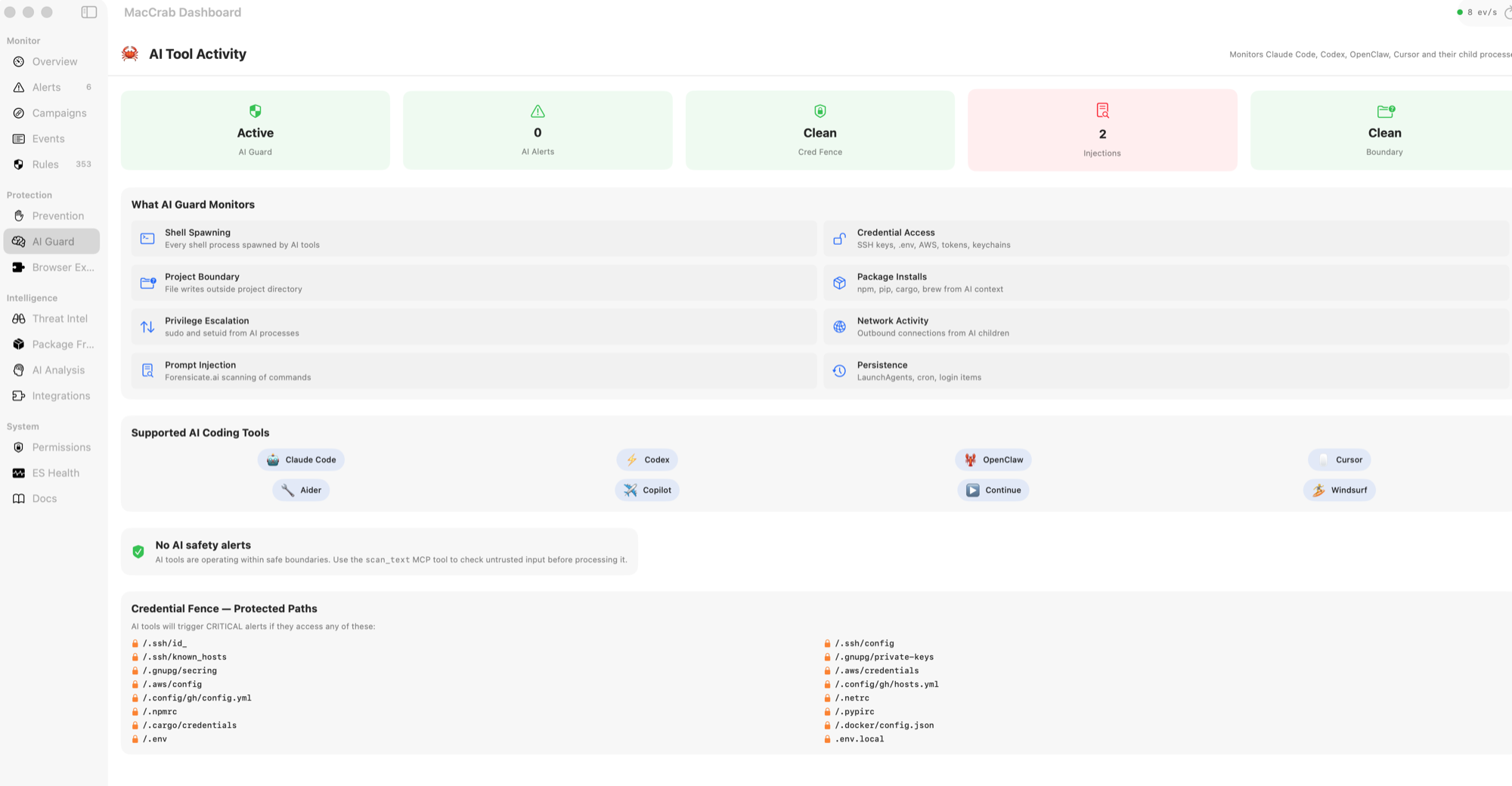
AI coding tool guardrails
Claude Code, Codex, Cursor, and Copilot are powerful — and sometimes they wander. MacCrab watches for credential reads, project-boundary escapes, prompt injection, and MCP server drift. Agent Data Lineage (new in v1.6.6) weaves each AI tool's LLM calls, subprocess spawns, file I/O, and network activity into one timeline — so you can see what your agent actually did, not just what it said to the model.